Use DMARC
The Domain-based Message Authentication, Reporting and Conformance (DMARC) protocol is designed to allow email systems to be protected from unauthorised use (or ‘email spoofing’).
DMARC extends the Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM) mechanisms, helping to detect forged sender addresses by:
- confirming the identity of the sender SPF and/or DKIM;
- instructing the user’s email system on how to manage emails that aren’t confirmed; and
- requesting reports from the email system to show the origin of email
To set up DMARC, you’ll need to add a TXT record in your DNS configuration. The Government Digital Service (GDS) has published guidance on using DMARC in your organisation here.
If you use Microsoft Office 365, the instructions to validate email in Office 365 can be found here.
If you use Google G Suite, the instructions to turn on DMARC can be found here.
The more DMARC is implemented, the better it becomes, so join in!
Make sure your email system is set up correctly
Whilst technology is only part of the answer to this, it is a part nonetheless.
Most email systems either have built-in protections, or are compatible with a range of filtering/blocking technology from third party suppliers, that check incoming emails for spam, phishing and malware. This allows the system to then block suspected phishing emails instead of delivering them to the user’s mailbox.
If you use Microsoft Office 365, follow their instructions to tune anti-phishing protection in Office 365.
If you use Google G Suite, follow their instructions to setup advanced phishing and malware protection.
Protect devices from malware
Whilst this is generally good security advice - it’s critical that all user devices are well protected from malware – it applies specifically to phishing too.
Many phishing emails hide malware within them or within the websites to which they attempt to direct the user. In some situations, this malware can do some (or all) of the job of collecting the sensitive information the attackers want.
A good endpoint anti-malware solution will provide protection from these issues. You can find out more about the SWGfL endpoint security services here.
Protect users from visiting malicious websites
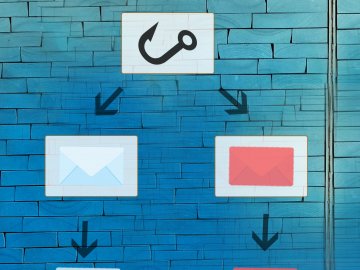
A phishing email will usually encourage a user to visit a malicious website, where the attacker will attempt to obtain sensitive information or deploy malware.
Many content filtering technologies, especially those used in schools, will be able to prevent users from accessing these websites, in the same way that they prevent access to websites containing other types of inappropriate content.
Like all the other technological measures, it cannot be 100% effective 100% of the time, but it will probably help.
Protect user accounts from misuse
One of the pieces of sensitive information attackers are commonly interested in is the access credentials for systems: the username and password.
Multi factor authentication involves adding at least one more authentication factor to the normal username and password (‘something you know’) login process, where the additional factors are either 'something you have' (like a one-time password sent in an SMS message) or 'something you are' (like a fingerprint).
Adding multi factor authentication typically involves the use of a third party service. However, this can protect user accounts from unauthorised access, even if an attacker does have the username and password.
Some general security controls also apply here, such as ensuring that elevated rights and permissions (e.g. ‘administrator’ accounts) are only used when needed and that user accounts for staff who no longer work for the organisation are disabled promptly. These general controls will help to defend you against phishing.