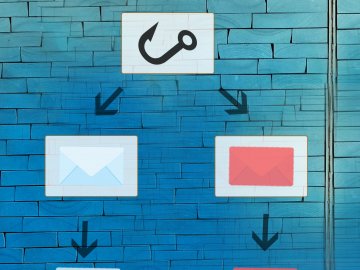
How Does Phishing Work?
Click the boxes below to learn more about the three stages of phishing.
Phishing: Stage 1
A website is created with functionality to collect information provided by users.
Sometimes this is a ‘clone’ of a genuine website, with malicious functionality added before it is published online.
Phishing: Stage 2
The phishing emails are created, with links taking users to the information-harvesting website.
Attachments may also be used as part of the phishing process, or to attempt to spread malware.
Phishing: Stage 3
The phishing emails are sent to the users.
Users clicking the links are directed to the website that was created at Stage 1. The website then gathers the information users provide.
What's the Point of Phishing?
The main purpose of phishing is to obtain personal data or sensitive information that cyber-criminals can use to carry out further attacks or commit fraud. By tricking individuals into revealing information voluntarily, attackers can bypass many technical security measures and gain access to systems, accounts, or financial resources much more easily.
The information collected through phishing can include usernames, passwords, banking details, credit card numbers, addresses, phone numbers, or security verification codes. Even small pieces of information can be valuable, as cyber-criminals often combine multiple details from different sources to build a more complete profile of a victim.
Ultimately, phishing is effective because it targets people rather than technology. By exploiting trust, curiosity, or a sense of urgency, cyber-criminals can persuade individuals to reveal information that helps them carry out more serious cyber crimes.
How Many People Are Affected by Phishing?
Phishing is one of the most common forms of cybercrime worldwide, affecting millions of individuals and organisations every year. The Anti-Phishing Working Group (APWG), an international coalition that tracks phishing activity, consistently reports extremely high numbers of phishing attempts and victims globally.
According to APWG reports, millions of phishing emails are sent every day, targeting both individuals and businesses. Because these phishing campaigns can be sent to thousands or even millions of people at once, even a small success rate can result in a large number of victims.
The numbers have shown to affect organisations across many sectors, including finance, education, healthcare, retail, and government services. Businesses are often targeted because compromising a single employee’s account can potentially provide access to internal systems, sensitive data, or financial processes.
Why is it Called Phishing?
It is called phishing because the practice was likened to fishing (angling). The email functioned as a sort of ‘bait’ or ‘lure’, and it only needed a few people to ‘bite’ to make it worthwhile.
It’s generally agreed that the earliest phishing attacks, in the mid-90s, targeted AOL users with attempts by cyber-criminals to steal account details and passwords.
The ‘ph’ in phishing replaces the ‘f’ from fishing in a reference to phreaking, a common hacking style in the late 60s and early 70s involving the manipulation of phones and phone networks.
What is Email Spoofing?
Email spoofing is when an email is sent with a forged or “spoofed” sender address, making it appear as though the message has come from someone else. This technique is commonly used by cyber-criminals to make a message look like it was sent by a trusted person or organisation, such as a bank, a well-known company, a colleague, or even a friend.
In many cases, the displayed sender name or email address in the message appears legitimate, even though the email was actually sent from a completely different source. For example, an attacker might send a message that appears to come from an organisation’s support team or from a manager within a company in order to persuade the recipient to open the message, click a link, or share sensitive information.
One reason email spoofing is possible is because the original email protocols used across the internet were not designed with strong security or authentication in mind. When email systems were first developed, they were intended to support open communication rather than defend against malicious activity. As a result, early email protocols did not include built-in mechanisms to verify that the sender address shown in an email genuinely belongs to the person or organisation that appears to have sent it.
Because of this limitation, attackers can manipulate parts of the email message to make it appear as though it originated from a trusted source, even though it did not. To help combat spoofing, modern email systems now use additional security technologies such as SPF, DKIM, and DMARC, which help verify whether an email has actually been sent from an authorised server. However, not all systems implement these protections fully, and attackers continue to find ways to exploit weaknesses.