Training
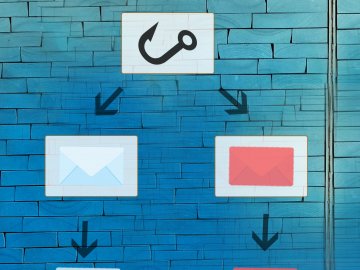
One of the most important steps is to help users identify phishing emails, and provide mechanisms or processes for reporting them.
Whilst many of us think we know what a phishing email looks like, there are many others that might not, so helping users to spot them is a key part of improving security. One aspect that’s often missed is what to do with it when you have spotted it, so make sure this is included in training.
Do bear in mind that, even with training, it’s generally not possible for users to spot them every time, so the other steps set out below are important too.
You can try the Sophos “Spot the Phish” game to have a look at a few example emails and decide whether they are genuine or phishing.
Check internal processes
Whilst phishing training is for all staff (as part of security awareness training), there are various processes that should be checked to ensure any weaknesses in certain areas of the operation can be addressed, and there may be additional training for certain teams arising from this.
A good place to start is with the normal procedures for parts of the organisation that are commonly a focus of phishing emails: finance operations and IT services. For example:
- What is the process for making normal payments (i.e. to suppliers), and for expediting payments should it be necessary? Does everyone involved know how it works, and therefore how to spot unusual requests?
- What is the process for dealing with technical support issues with the various platforms used by the school? Where email is used for this, how can the authenticity be verified?
Where possible, it’s a good idea to document these processes as simply as you can, and then work with everyone to make sure they’re followed.
Reconsider information published externally
Particularly for spear phishing and whaling attacks, publicly-available information about an organisation is part of what cyber-criminals use to design more effective phishing emails and deliver them to the correct victims.
It is therefore worth considering what visitors to your website do actually need to know, compared to detail that may be more useful to an attacker than to a genuine visitor.