Are Phishing Attacks All The Same?
In short, no. Understanding that phishing is not a single, one-size-fits-all threat is the first step toward recognising and defending against it. By exploring the different forms phishing can take (and the tactics attackers use) you can better identify suspicious activity and reduce the risk of falling victim.
This resource introduces the key types of phishing attacks, how they differ, and what to look out for, helping you build awareness and strengthen your security habits.
What is Spear Phishing?
Spear phishing is a phishing attack that is directed at a specific individual or organisation.
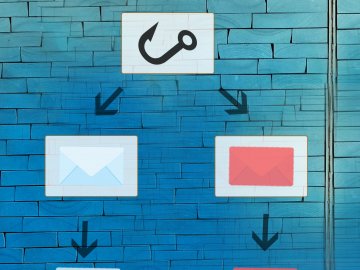
The definition of phishing includes the principle that the attack is based on a mass distribution of emails or messages. Users are not targeted individually, and there may be thousands of recipients.
Spear phishing, however, is a targeted attack. The attacker spends more time crafting the email, usually adding details that personalise it in some way (e.g. an attacker that knows, from public information, the place you work and a number of your colleagues, can create a spear phishing attack that uses these details to make it appear more legitimate).
As the distribution of a spear phishing attack is more targeted, it tends to be the case that the request is also specific. A common spear phishing attack requests that an employee performs a payment or transfer of funds of some type, by posing as a senior employee within the organisation.
What is Whaling?
Whaling is a spear phishing attack that is directed at a senior person within an organisation, like the CEO, Headteacher or governor.
Like spear phishing, whaling is usually a targeted attack, and the attacker typically spends more time preparing the attack than with a generic phishing attack. For this reason, whaling attacks can be difficult to spot.
Also called ‘CEO Fraud’, the total value of CEO scams increased by 11% from £11.6m in 2021 to £12.9m in 2022. Troublingly, as these attacks often involve an employee authorising a transaction using their real systems, it is usually not recoverable through the bank once the funds have been transferred, and the use offshore laundering and/or ‘money mules’ can make it difficult to trace, even for law enforcement agencies.
The best protection from a whaling attack, therefore, is vigilance: wherever possible, verify the authenticity of a request by actually speaking to the person via a known channel.
What is Smishing?
Smishing (short for SMS phishing) is a type of phishing attack that uses text messages to trick people into revealing sensitive information or taking harmful actions.
Attackers send a message that appears to come from a trusted source, such as a bank, delivery company, or government service. The message usually creates a sense of urgency and includes a link, phone number, or instruction.
What is Clone Phishing?
Clone phishing is when a cybercriminal copies a legitimate email you’ve already received and then re-sends it with a malicious change, usually with fake link or infected attachment.
Instead of creating a message from scratch, the attacker takes a real email (for example, a delivery notice or shared document) and makes it look almost identical.