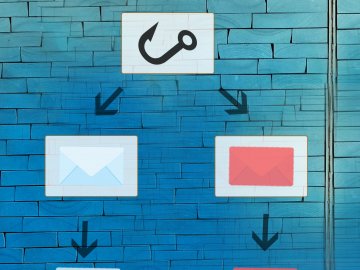
Phishing is a type of cyber attack in which a cyber-criminal attempts to trick someone into engaging with something malicious with the end goal being to reveal sensitive information. This is usually done by sending an email, text message, or other communication that encourages the recipient to click a link, download an attachment, or enter personal details on a website.
The goal of phishing is often to collect information such as usernames, passwords, banking details, personal information, or security codes. Criminals can then use this information to access accounts, steal money, commit identity fraud, or launch further attacks.
Phishing messages are typically designed to look genuine and trustworthy. Attackers often impersonate well-known organisations such as banks, delivery companies, government services, or online platforms. The emails and websites they create are carefully styled to resemble legitimate communications, using official logos, similar email addresses, and familiar formatting to make the message appear authentic.
These messages often create a sense of urgency or concern, for example claiming there is a problem with an account, a missed delivery, or a suspicious login attempt. By encouraging quick action, attackers hope recipients will respond without carefully checking whether the message is legitimate.
Phishing is a form of social engineering, meaning it relies on manipulating people rather than directly exploiting technical vulnerabilities. Instead of hacking systems, attackers attempt to influence individuals into performing actions they would not normally take, such as sharing private information or clicking unsafe links.